Contents
| Table of Contents | ||||||
|---|---|---|---|---|---|---|
|
...
- List Consent Receipts in your RN personal cloud: http://open-notice.github.io/respect-network-receipts/
...
- Consent notice details can be appended to the MVCR to accommodate different personal data sensitivity, data sharing and additional contextual compliance requirements.
- A context field is a field in the MVCR indicating that there are contextual conditions and exceptions to consent that can be listed and applied by an organisation to the context of receiving consent (e.g. medical emergency overrides). In the MVCR the context is a flag with yes or no. If yes, the provider is stating that they implement a check list of contextual consent requirements. Additional contexts can also be added to a consent receipt.
- Organisations can append trusted services links/icons to the receipt and further extend the assurance provided to capture multiple consent notice types e.g. cookie, terms of use.
Specification by example (SBE) is a collaborative approach to defining requirements and business-oriented functional tests for software products based on capturing and illustrating requirements using realistic examples instead of abstract statements. It is applied in the context of agile software development methods, in particular behavior-driven development. This approach is particularly successful for managing requirements and functional tests on large-scale projects of significant domain and organisational complexity.[1] (https://en.wikipedia.org/wiki/Behavior-driven_development)
...
| Field Name | Field Description | Field Purpose / Explanation | Reason Field is Required | Cloud Receipt Capture & Sign: Format example in (XDI) Note: following lines all prepended with ([=]!:uuid:1111/[+]!:uuid:9999) |
|---|---|---|---|---|
| Data Subject (DS) | Name or pseudonym of the Data Subject at minimum | Data Subject is primary party to consent | Data Subject is the consent contributor and primary party of the consent (which is why this is the first field of the MVCR) If not signed by Data Subject then its use post consent may be limited. | Data Subject: Alice [=]!:uuid:1111 |
| Address (and jurisdiction) of Data Controller (DC) | Name of the entity issuing the receipt | Should be the entity / organization in receiving the personal data and is responsible for consent compliance. | Is the Data Controller and the primary party responsible for administration of the consent and consent receipt | Data Controller: Amazon [+]!:uuid:9999 |
| Purpose | The purposes for which the personal information is being collected. | This is a single purpose at minimum linked to the short purpose notice, or policy of purpose. | A purpose notice is a basic and common legal requirement and functionally a requirement of consent. | [#receipt]!:uuid:1234[<#purpose>]<@0>&/&/"We need to process your payment." [#receipt]!:uuid:1234[<#purpose>]<@1>&/&/"We need your data to prevent fraud." [#receipt]!:uuid:1234[<#purpose>]<@2>&/&/"We will advertise to you." |
| Location of Consent | The location of the consent provision. from which the consent receipt originates.(For example the web page with the consent button. ) | This indicates the 'point of consent' - hopefully a button where the user clicked "I agree" or "I consent" (i.e. the biggest lie) Can be a URI, URL, URN, This can also be a physical space where surveillance legal notice requirements exist (EU) - Global Positioning System (GPS) |
| |
| Sensitive Personal Data Flag (Y/N) | Flag to categorise the information collected as sensitive or not (Y/N) | Each jurisdiction has classifications of sensitive personal information (privacy): The generally include health, financial, child protection (>14), youth protection(>19 or >22), educational, religious, Union categorisations | If Yes, then additional notice requirements are needed to confirm its compliance status. If No, then the consent is automatically compliant | |
Third Party Sharing | Flag whether data is shared with third parties. (Y/N) | If true, then compliance is dependent upon additional notice requirements not present in a MVCR. This can be addressed with the "Third Party Sharing" extension. | If Yes, then additional notice requirements are needed to confirm its compliance status. If No, then the consent is automatically compliant | |
| Timestamp | When consent was obtained | To record when the user, either by implication or explicity, granted consent for the purposes described. | ||
| Privacy Policy | The issuing entity's privacy policy (either inline copy, or reference to URI) | If not available, should provide a notice that it is missing | Is the minmum Policy (or short notice) Needed to create a consent receipt. | |
| Operational Context Flag | Flag wether the Operational Requirements are present or not. (Y/N/Unknown) | For the presentation of consent there are contextual and prescriptive requirements in legislation, a check list of these elements is being crated in this draft below. | Consent has contextual compliance requirements for the notice to be sufficent. These depend on the location and format of the consent notices An organisation displays agreement (or not) to implement these OC requirements and this is reflected on the consent receipt. |
...
Respect Network (RN) Technical Demo:
- Store a Consent Receipt in your RN personal cloud using XDI: http://amazon-respect-consent.herokuapp.com/
- List Consent Receipts in your RN personal cloud: http://open-notice.github.io/respect-network-receipts/
...
Amazon Respect Use Case: With the Respect Network and Open Notice
(Note: Amazon Respect is a Fictitious organisation used here only as an example)
(http://open-notice.github.io/consent-receipt/amazon-mock/signup.html)
Implementation of consent receipt which is signed & created by a DC and stored in a personal cloud.
...
Each field on a Minimum Viable Consent Receipt are there is included in response for legal to legal notice requirements, if . If legal requirements are present, a "yes" or "no" flag is added to consent record, further infrastructure is needed to record disputes to self asserted claims. the consent receipt.
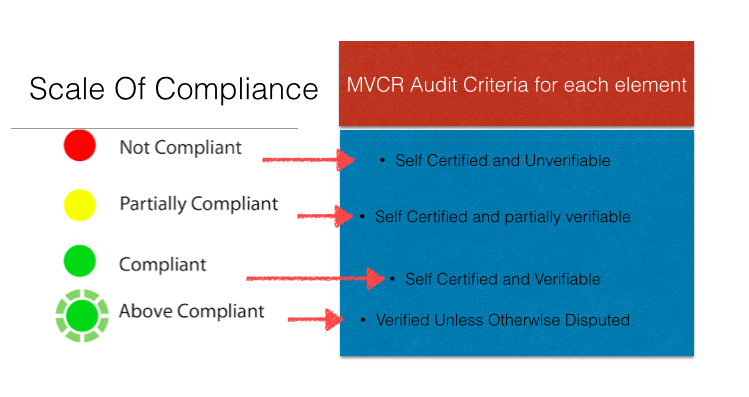
The MVCR has a maximum rating of "compliant. (Note: Additional " Additional Ratings e.g. "above compliant", "trusted", and "user managed" will be provide with extensions).
`A A compliant rating can be self asserted with within the provision of this consent receipt. A scale of compliance is used for each of these notice information elements. If one or more elements do not work, or are not verifiable, then a status of partialy "partially compliant" is provided. Further infrastructure is needed to record disputes to self asserted claims.
If all elements are not verifiable, then the consent is no longer compliant or verifiable for basic compliance level rating.
Notice Compliance Checklist | Non Compliant | Partially Compliant | Compliant | Above Compliant | Trusted | User Managed |
|---|---|---|---|---|---|---|
Contact of DC |
|
| X |
| ||
Address of DC |
|
| X |
| ||
Purpose(s) |
|
| X |
| ||
Sensitive Data (If NO) |
|
| X |
| ||
Share with 3rd Party (If No) |
|
| X |
| ||
| Agree to implement context checklist? (Y/N) | Yes | |||||
| Any of the items above self asserted is? Disputed or un-verifiable (Y/N Flag) (If No) ( if Yes and unresolved = Non-Compliant) | Y | XN |
(additional (NOTE: Additional architecture is needed to mediate compliance level ratings.)
MVCR Compliance Assurance Audit & Compliance Scale
Each item in the MVCR will be rated with this scale presented below
The compliance scale below is based on the ICO table of compliance located here from the UK Information Commissioner's Office: http://ico.org.uk/for_organisations/data_protection/working_with_the_ico/~/media/documents/library/Data_Protection/Detailed_specialist_guides/auditing_data_protection.pdfpd
Trusted Services Appendix
Trusted services/, networks and frameworks , can be used to meet or exceed notice (and therefore consent) legal requirements. Or to They may also address the need for assurance and trust for people so , in order that consent and its management can be automated and more usable. It is for seen that a notice registry is the natural place for trust services to register their services.
A process for auditing and verifying all trust services needs to be in place for trust services to be trustedtrustable. Then Then when an organisation enrols into the registry they can also add (or manage) trust services that has been added to the receipt.
This
...
table
...
maps the list and categories of assurance framework with examples and notes on interoperability
...
to a category of service.
Type of Trust Framework |
| Personal Policy Preference
| Consent Extension Location | Trusted Service Provider Examples | ||
|---|---|---|---|---|---|---|
Tracker: Analytics etc |
...
. | Cookie | Do Not Track | browser header | cookiepedia, privacy clearing warehouse, Ghostery | ||
Terms of Use Policy
| Agree to terms | TOS;DR, Citizen Me | ||||
Policy Tracking Services | Policy Comparison | Has terms materially changed ( is consent still compliant? ) | TOSBack | |||
Consent Type | What kind of consent has been received | To record the type of consent or whether there is an exception to the requirement for consent. | ||||
Reputation
| Trust Framework | (all trust services provide reputation) | ||||
Privacy Icons
| Pictorial Short Notices | Disconnect Me | ||||
Third Party Ratings
| Effect ratings from third parties | Disconnect Me | ||||
Capture of Personal Preference at Time of Consent | Does the issuing entity acknowledge DNT | If not available, should provide a notice that it is missing | ||||
Data Control Protocol | User Managed Access | |||||
Trusted Network Service | Respect Network | |||||
Standards | ||||||
Certificates | TrustE | |||||
Levels of Assurance | KI: Identity Assurance Framework |
Design Appendix:
Summary Design Goals to Assess: MVCR
...